Ledger Live Login — Secure Access to Your Crypto
A concise, practical guide to safely accessing Ledger Live and protecting the keys to your crypto assets.
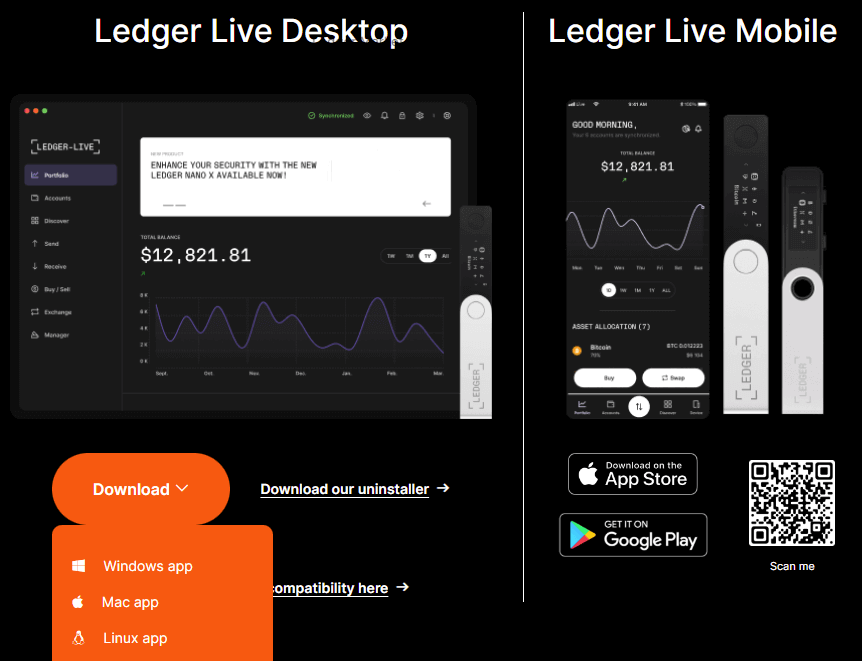
Logging in to Ledger Live is your gateway to managing cryptocurrencies securely from desktop or mobile. Ledger Live serves as the official companion app for Ledger hardware wallets, enabling you to view balances, send and receive assets, install apps, and connect to decentralized applications. Because Ledger Live acts as an interface to valuable assets, understanding how the login process works and adopting strong security habits is essential.
When you open Ledger Live, you’ll start at the app’s home screen and choose to unlock or connect your device. The recommended and most secure method is to pair a Ledger hardware device (such as a Ledger Nano S Plus or Ledger Nano X) via USB or Bluetooth. Your private keys never leave the hardware; Ledger Live simply reads public account data and helps you sign transactions through the device. This setup reduces exposure to phishing and remote compromise because the critical signing step happens inside the device’s secure element.
For users who prefer added convenience, Ledger Live can be used with third-party integrations like web3 apps or mobile features. However, convenience should not come at the cost of weaker protection. If you enable features that store a session or rely on cloud sync, confirm that you understand what data is synchronized and that two-factor authentication (2FA) and strong local device locks are enabled where possible.
A strong login practice begins outside Ledger Live itself. Keep your computer and mobile operating systems updated, run reputable antivirus software, and avoid running unknown browser extensions or applications that request access to your wallet or its files. If you are using Ledger Live on a shared or public computer, always log out and avoid saving credentials. Ledger Live doesn’t require a password to read public account data, but it will ask for action confirmation when performing sensitive tasks; treat those prompts as security checkpoints.
Your Recovery Phrase—often 24 words—is the ultimate backup of your crypto. Never enter it into any application or web page, and never share it. Ledger Live will never ask you to provide your recovery phrase over support email, chat, or social media. Store this phrase physically in a secure location, ideally using fireproof and waterproof metal backup options, and consider a geographically separated backup for additional redundancy. If anyone asks you to paste or type your recovery phrase to “verify” an account, it’s a scam.
When you sign in using your Ledger device, always confirm transaction details on the hardware screen itself. This step is critical: Ledger’s secure element displays the recipient address and amount for each transaction, ensuring that a compromised computer cannot silently modify the destination. If the hardware display looks scrambled, unexpected, or asks for input you don’t recognize, disconnect the device and consult official Ledger support channels.
Beware of phishing. Attackers commonly deploy convincing fake websites, emails, and social media messages that mimic Ledger branding to steal credentials or trick you into revealing your recovery phrase. Always validate the URL of any website and prefer direct links from Ledger’s official domain. Bookmark the official Ledger Live download page and install updates through the app or the official site rather than third-party sources. If you receive unsolicited messages claiming urgent action, treat them as suspicious until verified.
For teams or advanced users managing multiple accounts, create dedicated profiles within Ledger Live where possible and label accounts clearly. Keep an audit trail of significant changes—especially when transferring large balances—and consider multisig configurations for shared custody. Ledger supports advanced workflows through verified integrations; test with small transactions when configuring a new workflow.
If you lose access to your Ledger device, do not panic. Using your securely stored recovery phrase, you can restore access on another Ledger device or a compatible hardware wallet that supports the same standard. Restoration should be performed only on trusted hardware and never on unknown or suspect devices. After restoration, update firmware and software immediately and move funds to a new address if you suspect any compromise.
Privacy-conscious users should consider network and account hygiene. Use different accounts for distinct purposes—trading, long-term storage, or smart-contract interactions—and avoid reusing addresses across high-risk activities. Remember that blockchain transactions are public: use Ledger Live’s labeling for clarity, but assume on-chain activity is visible to others.
Finally, in case of technical issues or suspected compromise, use Ledger’s official support resources and community guides rather than third-party advice. Record software versions, connected device models, and exact error messages when contacting support to speed resolution. Keep backups of essential configuration files only if you understand the risk, and never back up private keys or recovery phrases to cloud providers or plain text documents.
Practical tip: Treat each login and transaction as a security event—verify, confirm, and protect. Stay informed: subscribe to Ledger’s official changelog for security bulletins, participate in community audits, and periodically review account permissions for dapps—small routine checks dramatically reduce long-term risk and update passwords and devices regularly.